
CYBER SECURITY
The global cyber threat continues to expand at a express pace, with a boosting number of data breaches each year. A report by one security expert revealed that a shocking 7.9 billion records have been exposed by data breaches in the first nine months of 2019 alone. These numbers are more than double (113%) the number of records exposed in the same period in 2018.
Learn More about servicesWHY CHOOSE US
Our robust security team will not only deliver the ultimate results but also give you every solution regarding your project security.




WEB-SECURITY & SSL CERTIFICATE
Any organization must install the SSL Certificate onto their web server to initiate a secure connection with the browsers. Once the secure session is established, all web traffic in between the web server and the web browser will be secure. SSL Certificate is a small data file that can digitally bind a cryptographic key with the organization’s details. When it is installed on any web server, it activates the padlock and the https protocol and allows secure connections from a web server to a browser. We also provide secured VPN for your private or personal use.




WEBSITE & APPLICATION VULNERABILITY ASSESSMENT
Vulnerability analyzing is the process to identify, classify and to define vulnerabilities in websites, computer systems, Servers, applications and network infrastructures and providing the organization doing the assessment with the necessary knowledge, awareness and risk background to understand the threats to its environment and react appropriately. It is a process to evaluate, and assess susceptibility to natural and technological hazards. After this assessment you will be able to secure your computer systems, networks, Websites or Web-applications.





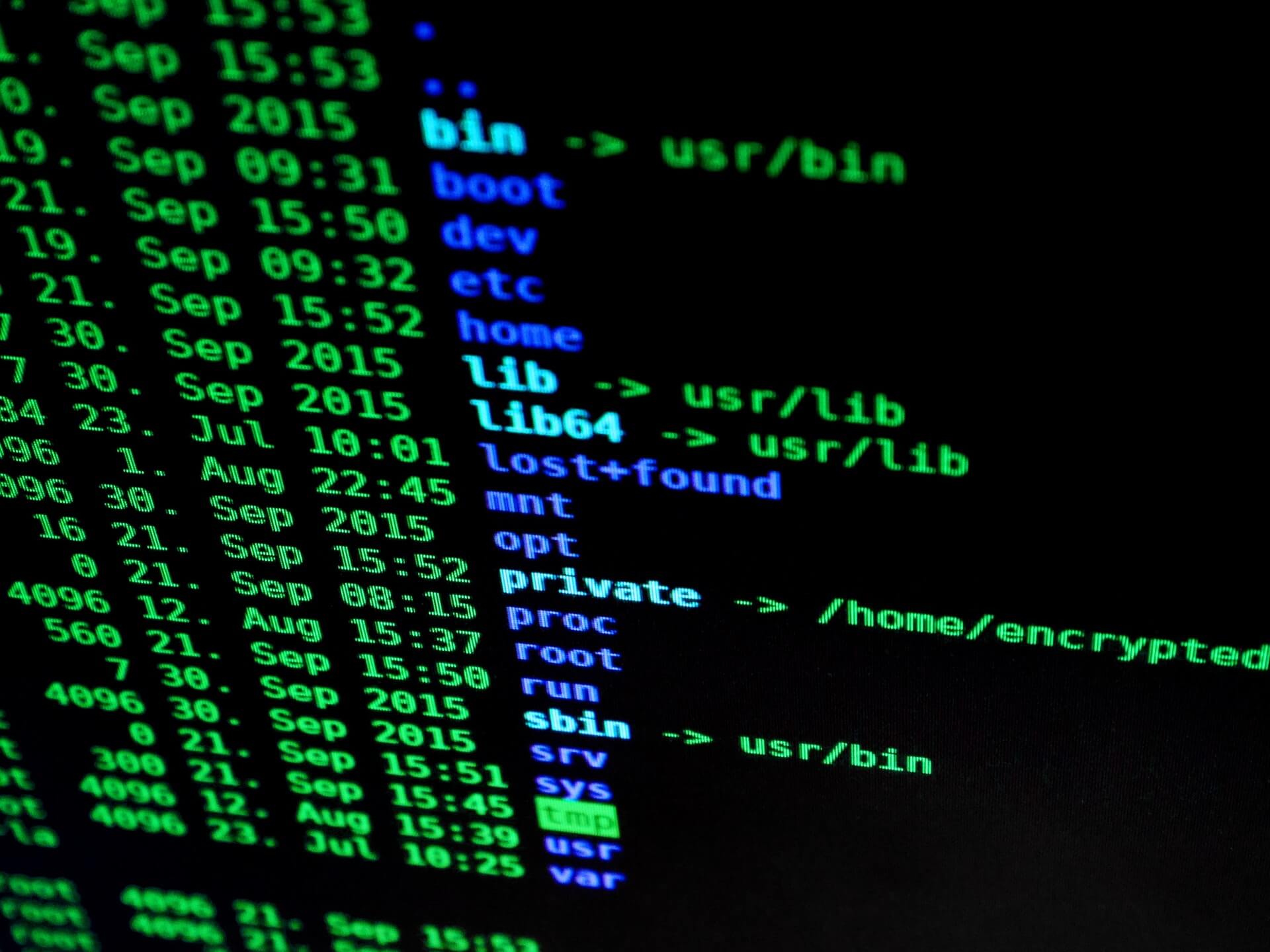
VULNERABILITY REPORTS
Once completing the Vulnerability scan, the socond step in the vulnerability assessment process is to write the report. This assessment on which the report is based is a common cyber-security measure to identify, analyze, and then rank vulnerabilities in systems or servers. Our team performs vulnerability assessments not only in websites or web-applications but also in other network infractructures, computer systems, and servers. The main steps of the assessment are to evaluate and define its risk level.
Enterprise
- Automotive
- Social
- Healthcare
Developer
- Developer Network
- MetaProton Developer
Company
- Careers
- About MetaProton